While I consider myself a long way from being an absolute master, I think I have more experience with Microsoft
Continue readingMonth: November 2022
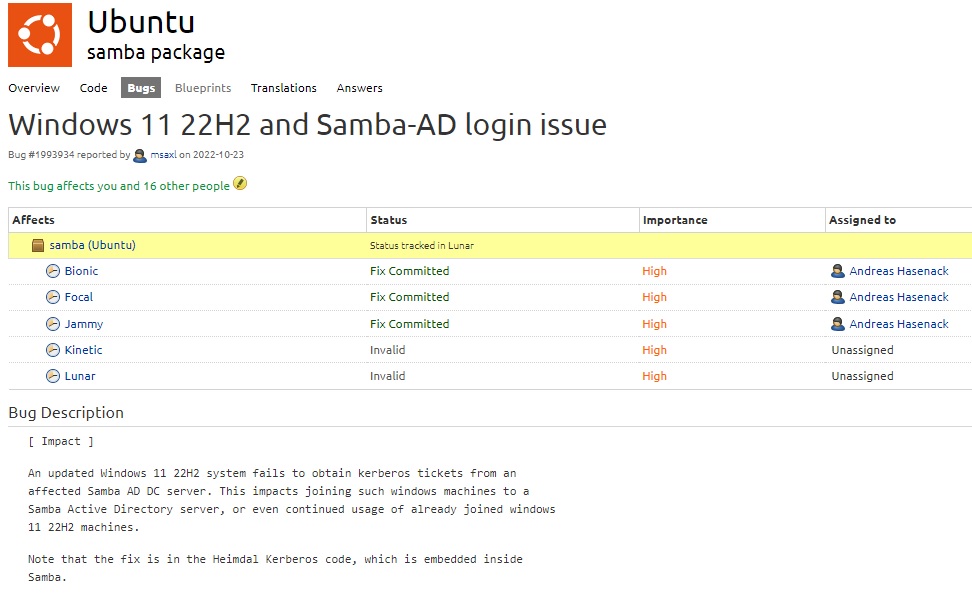
Windows 22H2 repeatedly says “wrong username and password” trying to login Active Directory user
I recently had to troubleshoot an issue where a new Surface Pro 9 for an employee of an existing company.
Continue reading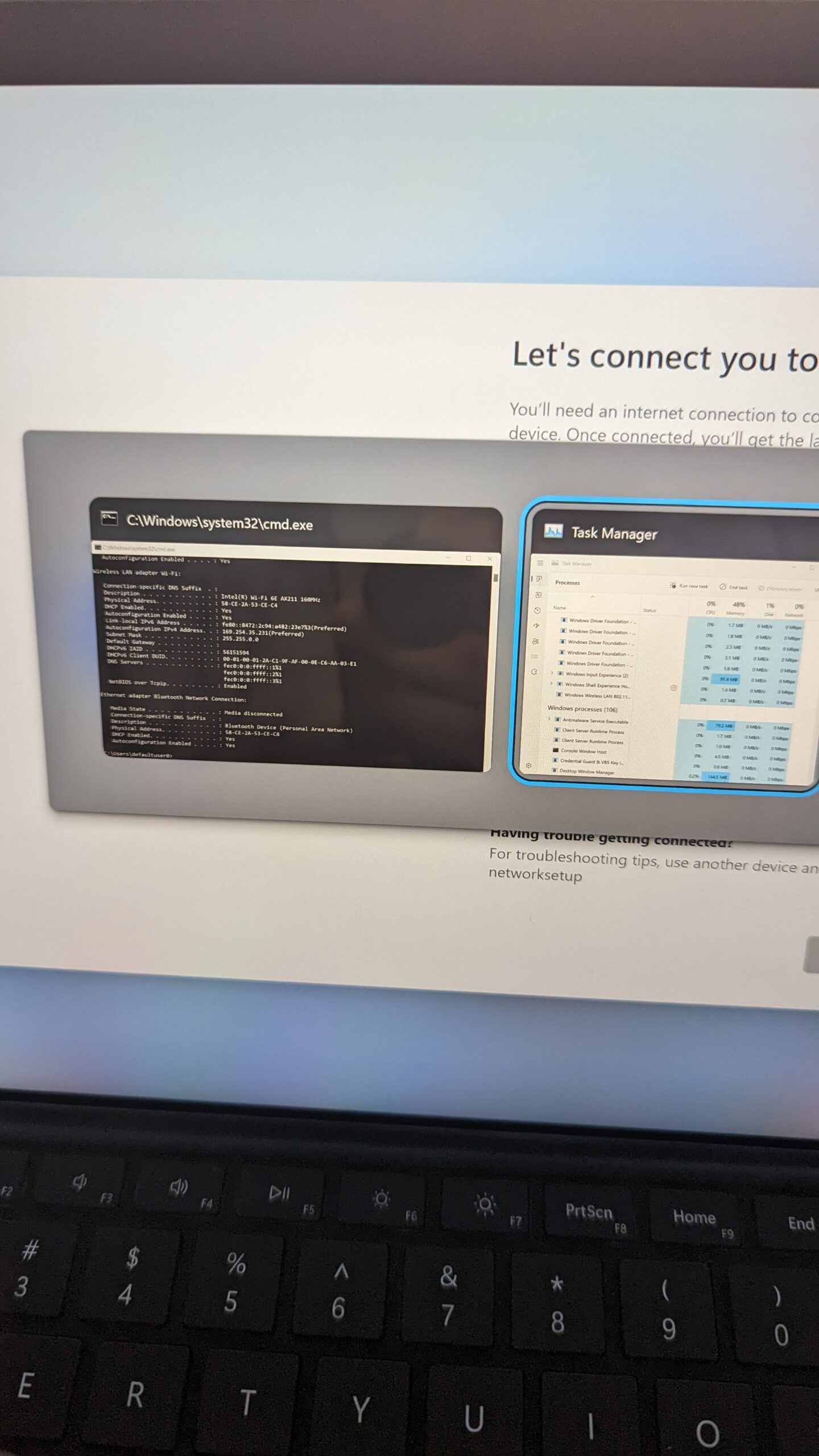
Gaining Command Prompt access on a Windows Computer that has never been set up
I sometimes work in an environment that has reasonably tight security requirements. One of those requirements as that a device’s
Continue reading