This thing is nasty. I’ve seen what I can only believe is a variant of WORM_VOBFUS.SMIS as defined by Trend Micro. Here’s what’s happening: an infected computer on your network looks for any shared folders (network shares, USB flash drives, etc…) and hides all of your real files. It then will replace the “hidden” files, with .EXE’s of the same names, to try and trick people in to clicking on them, and causing the worm to spread further. I’ve already seen this thing a few times and have developed a good plan of action for fighting it off.
Finding the infected computer and Cleaning the Infection
Skip ahead if you want to unhide your files, but I want to cover this virus a little further in depth. The hard part: Try to identify what user(s) may have been infected and caused this issue in the first place. As of 12/13, several AV vendors are beginning to detect this as a worm, but make sure you, at a minimum you at least have everyone scan their computers with something like Trend Housecall. If your antivirus programs have heuristics, set them to log “probable malware” and crank the heuristics to high. This thing behaves like a worm, and even if your antivirus application hasn’t been updated for this specific mutation, it’s pretty easy for a good antivirus program to spot.
To try and pin point the computer that brought the infection to your doorstep, check the local user directories of each user. For example, if you log in as “ASmith” on your computer, check C:\users\ASmith – or in Windows XP, check C:\Documents and Settings\ASmith. If you see a file named either Google.com or MSN.com (or pretty much any .com file), delete it. You’ve found your guilty party, and the file that keeps causing havoc.
Unhiding the Hidden Files
Now, let’s say you’ve already been hit. On a workstation where your icons all disappear, you traditionally run Unhide.exe – but since these files are in a file share on a server, you’re going to need to do this manually. It’s okay, I’ll help! Now, we can’t just “unhide” the files, because they’ve been marked as SYSTEM files as well (you can see the checkbox below the hidden attribute is “System” – which is also grayed out) – so we’ll have to change the “System” or “S” attribute, as well as the hidden, or “H” attribute.
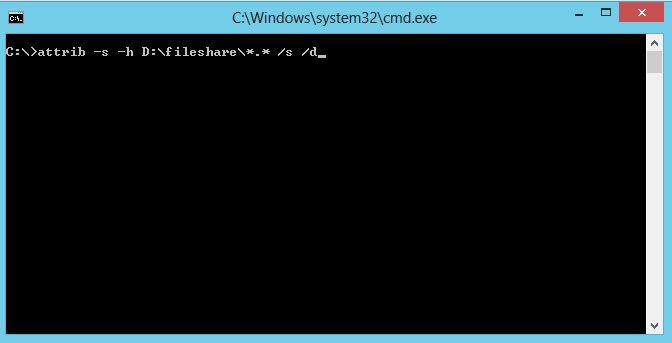
To unhide all of the folders, subfolders, and files within the share, you must run this command from the server. Replace D:\Fileshare with the local path to the shared folder (remember, even if your share is called “\\servername\sharename” the share might be D:\fileshare on the server).
Unhide the folders, subfolders, and files within the shared folder:
attrib -s -h D:\fileshare\*.* /s /d
Then, to unhide the folder itself:
attrib -s -h D:\fileshare
Finally, it’s important to know that this thing loves to spread through thumb drives (flash drives, USB drives, whatever you want to call them). One of your best bets at catching it, apart from upping the paranoia level of your antivirus application, is to take a computer OFF of your network, and plug in every thumb drive you can get your hands on. Once you find a drive that has an Autorun.inf, you’ve found what is most likely the infected drive.
If you know your way around Group Policy and you’re administering a domain, you should also disable autorun from USB drives. Best of luck.